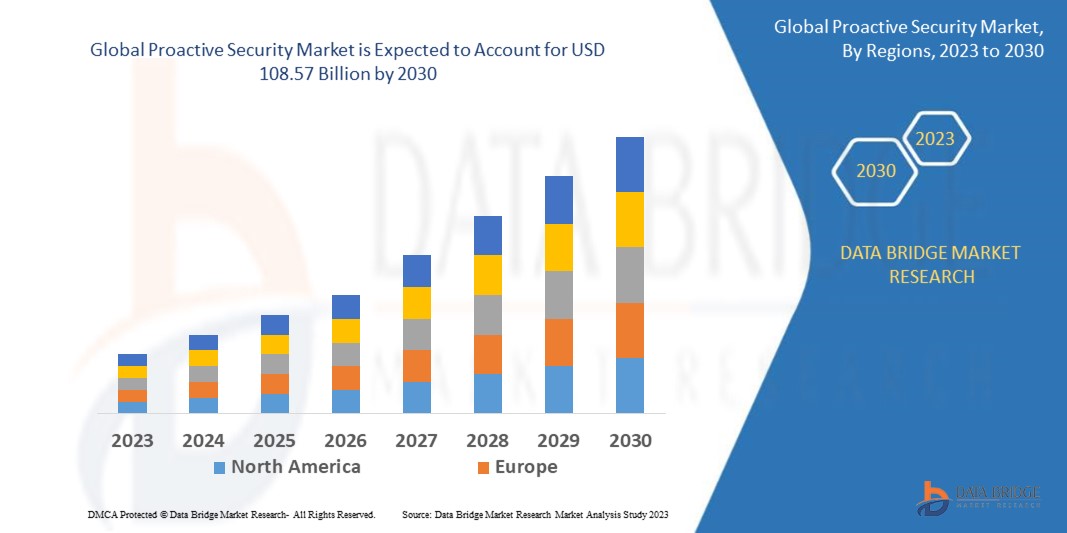
Global Proactive Security Market
Market Size in USD Billion
CAGR :
% 
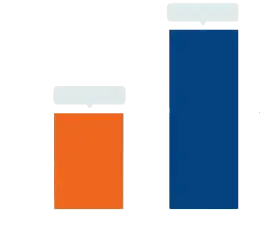 USD
32.55 Billion
USD
108.57 Billion
2022
2030
USD
32.55 Billion
USD
108.57 Billion
2022
2030
| 2023 –2030 | |
| USD 32.55 Billion | |
| USD 108.57 Billion | |
|
|
|
|
Proactive Security Market Analysis and Size
The growing number of data breaches and cyber-attacks are the major factors that positively influence the proactive security market. As companies shift their operations into digital form, the need for proactive security measures has become high. This has increased the demand for proactive security solutions such as security analytics, threat intelligence, and incident response. Furthermore, companies are investing in proactive security solutions such as security monitoring and analytics, risk and vulnerability assessment, and advanced malware protection to prevent any dangers before they occur, which will likely enhance the proactive security market.
Data Bridge Market Research analyses that the proactive security market is expected to reach USD 108.57 billion by 2030, which was USD 32.55 billion in 2022, at a CAGR of 16.25% during the forecast period. In addition to the market insights such as market value, growth rate, market segments, geographical coverage, market players, and market scenario, the market report curated by the Data Bridge Market Research team includes in-depth expert analysis, import/export analysis, pricing analysis, production consumption analysis, and pestle analysis.
Proactive Security Market Scope and Segmentation
|
Report Metric |
Details |
|
Forecast Period |
2023 to 2030 |
|
Base Year |
2022 |
|
Historic Years |
2021 (Customizable to 2015 - 2020) |
|
Quantitative Units |
Revenue in USD Billion, Volumes in Units, Pricing in USD |
|
Segments Covered |
Component (Solutions, Services), Organization Size (Large Enterprises, Small and Medium-Sized Enterprises), Industry Vertical (Banking, Financial Services, and Insurance; Government and Defence, Retail and E-commerce, IT and Telecom, Healthcare and Life Sciences, Energy and Utilities, Manufacturing, Others) |
|
Countries Covered |
U.S., Canada and Mexico in North America, Germany, France, U.K., Netherlands, Switzerland, Belgium, Russia, Italy, Spain, Turkey, Rest of Europe in Europe, China, Japan, India, South Korea, Singapore, Malaysia, Australia, Thailand, Indonesia, Philippines, Rest of Asia-Pacific (APAC) in the Asia-Pacific (APAC), Saudi Arabia, U.A.E, Israel, Egypt, South Africa, Rest of Middle East and Africa (MEA) as a part of Middle East and Africa (MEA), Brazil, Argentina and Rest of South America as part of South America |
|
Market Players Covered |
IBM (U.S.), Capgemini (France), Cisco Systems Inc. (U.S.), Palo Alto Networks (U.S.), Securonix (U.S.), LogRhythm, Inc. (U.K.), Rapid7 (U.S.), Broadcom (U.S.), Imperva (U.S.), FireEye, Inc. (U.S.), McAfee, LLC (U.S.), Oracle (U.S), AT&T Intellectual Property. (U.S.), Fujitsu (Japan), Trustwave Holdings, Inc. (U.S.), RSA Security LLC (U.S.), BlackBerry Limited (Canada) |
|
Market Opportunities |
|
Market Definition
Proactive security is used for prevention against major cybersecurity instances before they happen. Organizations can efficiently secure their important information from data breaches with proactive security solutions. Proactive security helps organizations to easily manage security vulnerabilities, optimize their security infrastructure, and control all their security products from a single platform.
Global Proactive Security Market
Drivers
- A growing number of cyber-attacks widens the market scope
The growing number of cyber-attacks, security breaches, and other cyber threats will likely boost the demand for proactive security. Progressing data breaches that result in high recovery costs and an increasing number of connected devices across enterprises due to the IoT implementation have encouraged businesses to shift towards proactive security solutions.
- Increasing demand for proactive security in the BFSI sector
The BFSI is one of the fastest-growing sectors in the proactive security market because BFSI companies have stringent regulatory and legal compliances associated with information security. According to data from the Financial Conduct Authority (FCA), the number of cyber-attacks against financial services companies augmented by more than 80 percent in 2018. As that cyber-attacks have a direct impact on market growth, financial service providers are likely to strengthen their security solutions by the usage of proactive security. This factor is likely to propel the growth of the market.
Opportunities
- Growing penetration of cloud technology
The increasing usage of cloud technology will surge the demand for proactive security and create ample market growth opportunities during the forecast period. Cloud-based identity verification solutions allow organizations to lessen costs while improving business alertness. With the advancement of cloud technology, businesses are digitizing, and stringent regulations such as PCI DSS, GDPR, and others are being enforced to protect IT systems from hacking attacks and data breaches. As a result of these compliances and regulations, enterprises are implementing efficient security solutions, and the proactive security market will expand rapidly in the upcoming years.
- Increasing demand for risk and vulnerability management solutions
The risk and vulnerability management solution is projected to create lucrative market growth opportunities. Risk and vulnerability management aids enterprises in identifying the existing cybersecurity posture of their information infrastructure and systems. Risk and vulnerability management solutions, such as proactive security solutions, have witnessed tremendous growth because of their features that offer direction to assess risks associated with evolving threats and security weaknesses. Hence, increasing demand for risk and vulnerability management solutions boosts the market growth.
Restraints
- Complexities associated with the implementation of proactive security
The complexities associated with implementing proactive security are major factors that will impede the growth of the proactive security market. The major complexities are to get proper visibility of all your assets, connect the security solutions accurately, and many others. These factors may hamper the market growth during the forecast period.
- Inadequate awareness regarding the benefits of proactive security systems
A lack of awareness regarding the benefits of proactive security systems may obstruct the adoption of proactive security systems and solutions during the forecast period. The advantages of a proactive security system allow teams to arrange tasks more competently, leading to much faster risk reduction. As a result, these factors are expected to be the major restraints on the proactive security market's growth.
This proactive security market report provides details of new recent developments, trade regulations, import-export analysis, production analysis, value chain optimization, market share, impact of domestic and localized market players, analyses opportunities in terms of emerging revenue pockets, changes in market regulations, strategic market growth analysis, market size, category market growths, application niches and dominance, product approvals, product launches, geographic expansions, technological innovations in the market. To gain more info on the proactive security market contact Data Bridge Market Research for an Analyst Brief, our team will help you take an informed market decision to achieve market growth.
Recent Development
- In 2019, Cygilant announced a merger with AT&T Cybersecurity Partner Program to support AlienVault USM Anywhere clients with managed security services. As a part of AT&T Cybersecurity's program, Cygilant assigns enthusiastic Cybersecurity Advisors who become completely familiar with customers' systems, compliance requirements, processes, and security goals.
- In 2019, RSA revealed the newest version of its market-leading SIEM named RSA NetWitness Platform, which features machine learning (ML) models based on deep endpoint observations to speedily detect anomalies in user behavior. This announcement helps customers to take a unified approach to managing digital risk.
Global Proactive Security Market Scope
The proactive security market is segmented on the basis of component, organization size and industry vertical. The growth amongst these segments will help you analyze meagre growth segments in the industries and provide the users with a valuable market overview and market insights to help them make strategic decisions for identifying core market applications.
Component
- Solutions
- Risk and Vulnerability Management
- Advanced Malware Protection
- Security Analytics
- Security Monitoring
- Security Orchestration
- Attack Simulation.
- Services
- Professional services
- Training and Education Services
- Support and Maintenance Services
- Consulting Services
- Design and Integration Services
- Managed Services
Organization Size
- Large Enterprises
- Small and Medium-Sized Enterprises
Industry Vertical
- Banking, Financial Services, and Insurance
- Government and Defence
- Retail and E-commerce
- IT and Telecom
- Healthcare and Life Sciences
- Energy and Utilities
- Manufacturing
- Others
- Travel and Hospitality
- Media and Entertainment
- Education
Proactive Security Market Regional Analysis/Insights
The proactive security market is analyzed and market size insights and trends are provided by country, component, organization size and industry vertical as referenced above.
The countries covered in the proactive security market report are U.S., Canada and Mexico in North America, Germany, France, U.K., Netherlands, Switzerland, Belgium, Russia, Italy, Spain, Turkey, Rest of Europe in Europe, China, Japan, India, South Korea, Singapore, Malaysia, Australia, Thailand, Indonesia, Philippines, Rest of Asia-Pacific (APAC) in the Asia-Pacific (APAC), Saudi Arabia, U.A.E, Israel, Egypt, South Africa, Rest of Middle East and Africa (MEA) as a part of Middle East and Africa (MEA), Brazil, Argentina and Rest of South America as part of South America.
North America dominates the proactive security market owing to the increasing cyber-attack cases in this region. Furthermore, the growing adoption of advanced technology and cybersecurity solutions will further boost the market growth in this region.
Asia-Pacific will continue to project the highest compound annual growth rate during the forecast period of 2023-2030 because of the growing adoption of advanced services in numerous organizations in this region. Furthermore, increasing demand for cloud-based solutions will further boost the market growth in this region.
The country section of the report also provides individual market impacting factors and changes in market regulation that impact the current and future trends of the market. Data points like down-stream and upstream value chain analysis, technical trends and porter's five forces analysis, case studies are some of the pointers used to forecast the market scenario for individual countries. Also, the presence and availability of Global brands and their challenges faced due to large or scarce competition from local and domestic brands, impact of domestic tariffs and trade routes are considered while providing forecast analysis of the country data.
Competitive Landscape and Proactive Security Market Share Analysis
The proactive security market competitive landscape provides details by competitor. Details included are company overview, company financials, revenue generated, market potential, investment in research and development, new market initiatives, Global presence, production sites and facilities, production capacities, company strengths and weaknesses, product launch, product width and breadth, application dominance. The above data points provided are only related to the companies' focus related to proactive security market.
Some of the major players operating in the proactive security market are:
- IBM (U.S.)
- Capgemini (France)
- Cisco Systems Inc. (U.S.)
- Palo Alto Networks (U.S.)
- Securonix (U.S.)
- LogRhythm, Inc. (U.K.)
- Rapid7 (U.S.)
- Broadcom (U.S.)
- Imperva (U.S.)
- FireEye, Inc. U.S.)
- McAfee, LLC (U.S.)
- Oracle (U.S)
- AT&T Intellectual Property. (U.S.)
- Fujitsu (Japan)
- Trustwave Holdings, Inc. (U.S.)
- RSA Security LLC (U.S.)
- BlackBerry Limited (Canada)
SKU-
Get online access to the report on the World's First Market Intelligence Cloud
- Interactive Data Analysis Dashboard
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
- Harness the Power of Benchmark Analysis for Comprehensive Competitor Tracking
Table of Content
1. INTRODUCTION
1.1 OBJECTIVES OF THE STUDY
1.2 MARKET DEFINITION
1.3 OVERVIEW OF GLOBAL PROACTIVE SECURITY MARKET
1.4 CURRENCY AND PRICING
1.5 LIMITATION
1.6 MARKETS COVERED
2. MARKET SEGMENTATION
2.1 KEY TAKEAWAYS
2.2 ARRIVING AT THE GLOBAL PROACTIVE SECURITY MARKET
2.3 VENDOR POSITIONING GRID
2.4 TECHNOLOGY LIFE LINE CURVE
2.5 MARKET GUIDE
2.6 MULTIVARIATE MODELLING
2.7 TOP TO BOTTOM ANALYSIS
2.8 STANDARDS OF MEASUREMENT
2.9 VENDOR SHARE ANALYSIS
2.10 DATA POINTS FROM KEY PRIMARY INTERVIEWS
2.11 DATA POINTS FROM KEY SECONDARY DATABASES
2.12 GLOBAL PROACTIVE SECURITY MARKET: RESEARCH SNAPSHOT
2.13 ASSUMPTIONS
3. MARKET OVERVIEW
3.1 DRIVERS
3.2 RESTRAINTS
3.3 OPPORTUNITIES
3.4 CHALLENGES
4. EXECUTIVE SUMMARY
5. PREMIUM INSIGHTS
5.1 PORTERS FIVE FORCES
5.2 REGULATORY STANDARDS
5.3 TECHNOLOGICAL LANDSCAPE
5.4 VALUE CHAIN ANALYSIS
5.5 COMPANY COMPARITIVE ANALYSIS
5.6 KEY STRATEGIC INITIATIVES
5.7 PATENT ANALYSIS
6. GLOBAL PROACTIVE SECURITY MARKET, BY OFFERING
6.1 OVERVIEW
6.2 SOLUTION
6.2.1 SECURITY MONITORING
6.2.2 SECURITY ANALYTICS
6.2.3 RISK AND VULNERABILITY MANAGEMENT
6.2.4 ATTACK SIMULATION
6.2.5 SECURITY ORCHESTRATION
6.2.6 ADVANCED MALWARE PROTECTION (AMP)
6.2.7 VIDEO MANAGEMENT SYSTEM
6.2.7.1. BY TECHNOLOGY
6.2.7.1.1. ANALOG BASED VMS
6.2.7.1.2. IP BASED VMS
6.3 SERVICES
6.3.1 MANAGED SERVICES
6.3.2 PROFESSIONAL SERVICES
6.3.2.1. CONSULTING
6.3.2.2. DESIGNING
6.3.2.3. TRAINING AND EDUCATION
6.3.2.4. INTEGRATION AND IMPLEMENTATION
6.3.2.5. SUPPORT AND MAINTENANCE
7. GLOBAL PROACTIVE SECURITY MARKET, BY DEPLOYMENT MODEL
7.1 OVERVIEW
7.2 CLOUD
7.3 ON PREMISES
8. GLOBAL PROACTIVE SECURITY MARKET, BY ORGANIZATION SIZE
8.1 OVERVIEW
8.2 LARGE ENTERPRISES
8.2.1 BY DEPLOYMENT MODEL
8.2.1.1. CLOUD
8.2.1.2. ON PREMISES
8.3 SMALL AND MEDIUM SIZED ENTERPRISE (SMES)
8.3.1 BY DEPLOYMENT MODEL
8.3.1.1. CLOUD
8.3.1.2. ON PREMISES
9. GLOBAL PROACTIVE SECURITY MARKET, BY END USER
9.1 OVERVIEW
9.2 GOVERNMENT AND DEFENSE
9.2.1 BY OFFERING
9.2.1.1. SOLUTION
9.2.1.1.1. SECURITY MONITORING
9.2.1.1.2. SECURITY ANALYTICS
9.2.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.2.1.1.4. ATTACK SIMULATION
9.2.1.1.5. SECURITY ORCHESTRATION
9.2.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.2.1.1.7. VIDEO MANAGEMENT SYSTEM
9.2.1.2. SERVICES
9.2.1.2.1. MANAGED SERVICES
9.2.1.2.2. PROFESSIONAL SERVICES
9.3 BANKING, FINANCIAL SERVICES AND INSURANCE (BFSI)
9.3.1 BY OFFERING
9.3.1.1. SOLUTION
9.3.1.1.1. SECURITY MONITORING
9.3.1.1.2. SECURITY ANALYTICS
9.3.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.3.1.1.4. ATTACK SIMULATION
9.3.1.1.5. SECURITY ORCHESTRATION
9.3.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.3.1.1.7. VIDEO MANAGEMENT SYSTEM
9.3.1.2. SERVICES
9.3.1.2.1. MANAGED SERVICES
9.3.1.2.2. PROFESSIONAL SERVICES
9.4 IT AND TELECOMMUNICATION
9.4.1 BY OFFERING
9.4.1.1. SOLUTION
9.4.1.1.1. SECURITY MONITORING
9.4.1.1.2. SECURITY ANALYTICS
9.4.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.4.1.1.4. ATTACK SIMULATION
9.4.1.1.5. SECURITY ORCHESTRATION
9.4.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.4.1.1.7. VIDEO MANAGEMENT SYSTEM
9.4.1.2. SERVICES
9.4.1.2.1. MANAGED SERVICES
9.4.1.2.2. PROFESSIONAL SERVICES
9.5 MANUFACTURING
9.5.1 BY OFFERING
9.5.1.1. SOLUTION
9.5.1.1.1. SECURITY MONITORING
9.5.1.1.2. SECURITY ANALYTICS
9.5.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.5.1.1.4. ATTACK SIMULATION
9.5.1.1.5. SECURITY ORCHESTRATION
9.5.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.5.1.1.7. VIDEO MANAGEMENT SYSTEM
9.5.1.2. SERVICES
9.5.1.2.1. MANAGED SERVICES
9.5.1.2.2. PROFESSIONAL SERVICES
9.6 HEALTHCARE AND LIFE SCIENCES
9.6.1 BY OFFERING
9.6.1.1. SOLUTION
9.6.1.1.1. SECURITY MONITORING
9.6.1.1.2. SECURITY ANALYTICS
9.6.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.6.1.1.4. ATTACK SIMULATION
9.6.1.1.5. SECURITY ORCHESTRATION
9.6.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.6.1.1.7. VIDEO MANAGEMENT SYSTEM
9.6.1.2. SERVICES
9.6.1.2.1. MANAGED SERVICES
9.6.1.2.2. PROFESSIONAL SERVICES
9.7 RETAIL AND E-COMMERCE
9.7.1 BY OFFERING
9.7.1.1. SOLUTION
9.7.1.1.1. SECURITY MONITORING
9.7.1.1.2. SECURITY ANALYTICS
9.7.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.7.1.1.4. ATTACK SIMULATION
9.7.1.1.5. SECURITY ORCHESTRATION
9.7.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.7.1.1.7. VIDEO MANAGEMENT SYSTEM
9.7.1.2. SERVICES
9.7.1.2.1. MANAGED SERVICES
9.7.1.2.2. PROFESSIONAL SERVICES
9.8 MEDIA AND ENTERTAINMENT
9.8.1 BY OFFERING
9.8.1.1. SOLUTION
9.8.1.1.1. SECURITY MONITORING
9.8.1.1.2. SECURITY ANALYTICS
9.8.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.8.1.1.4. ATTACK SIMULATION
9.8.1.1.5. SECURITY ORCHESTRATION
9.8.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.8.1.1.7. VIDEO MANAGEMENT SYSTEM
9.8.1.2. SERVICES
9.8.1.2.1. MANAGED SERVICES
9.8.1.2.2. PROFESSIONAL SERVICES
9.9 ENERGY AND UTILITIES
9.9.1 BY OFFERING
9.9.1.1. SOLUTION
9.9.1.1.1. SECURITY MONITORING
9.9.1.1.2. SECURITY ANALYTICS
9.9.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.9.1.1.4. ATTACK SIMULATION
9.9.1.1.5. SECURITY ORCHESTRATION
9.9.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.9.1.1.7. VIDEO MANAGEMENT SYSTEM
9.9.1.2. SERVICES
9.9.1.2.1. MANAGED SERVICES
9.9.1.2.2. PROFESSIONAL SERVICES
9.10 TRAVEL AND HOSPITALITY
9.10.1 BY OFFERING
9.10.1.1. SOLUTION
9.10.1.1.1. SECURITY MONITORING
9.10.1.1.2. SECURITY ANALYTICS
9.10.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.10.1.1.4. ATTACK SIMULATION
9.10.1.1.5. SECURITY ORCHESTRATION
9.10.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.10.1.1.7. VIDEO MANAGEMENT SYSTEM
9.10.1.2. SERVICES
9.10.1.2.1. MANAGED SERVICES
9.10.1.2.2. PROFESSIONAL SERVICES
9.11 EDUCATION
9.11.1 BY OFFERING
9.11.1.1. SOLUTION
9.11.1.1.1. SECURITY MONITORING
9.11.1.1.2. SECURITY ANALYTICS
9.11.1.1.3. RISK AND VULNERABILITY MANAGEMENT
9.11.1.1.4. ATTACK SIMULATION
9.11.1.1.5. SECURITY ORCHESTRATION
9.11.1.1.6. ADVANCED MALWARE PROTECTION (AMP)
9.11.1.1.7. VIDEO MANAGEMENT SYSTEM
9.11.1.2. SERVICES
9.11.1.2.1. MANAGED SERVICES
9.11.1.2.2. PROFESSIONAL SERVICES
9.12 OTHERS
10. GLOBAL PROACTIVE SECURITY MARKET, BY REGION
10.1 GLOBAL PROACTIVE SECURITY MARKET, (ALL SEGMENTATION PROVIDED ABOVE IS REPRESENTED IN THIS CHAPTER BY COUNTRY)
10.1.1 NORTH AMERICA
10.1.1.1. U.S.
10.1.1.2. CANADA (INCLUDING ONTARIO)
10.1.1.3. MEXICO
10.1.2 EUROPE
10.1.2.1. GERMANY
10.1.2.2. FRANCE
10.1.2.3. U.K.
10.1.2.4. ITALY
10.1.2.5. SPAIN
10.1.2.6. RUSSIA
10.1.2.7. TURKEY
10.1.2.8. BELGIUM
10.1.2.9. NETHERLANDS
10.1.2.10. SWITZERLAND
10.1.2.11. SWEDEN
10.1.2.12. DENMARK
10.1.2.13. POLAND
10.1.2.14. REST OF EUROPE
10.1.3 ASIA PACIFIC
10.1.3.1. JAPAN
10.1.3.2. CHINA
10.1.3.3. SOUTH KOREA
10.1.3.4. INDIA
10.1.3.5. AUSTRALIA AND NEW ZEALAND
10.1.3.6. SINGAPORE
10.1.3.7. THAILAND
10.1.3.8. MALAYSIA
10.1.3.9. INDONESIA
10.1.3.10. PHILIPPINES
10.1.3.11. TAIWAN
10.1.3.12. VIETNAM
10.1.3.13. REST OF ASIA PACIFIC
10.1.4 SOUTH AMERICA
10.1.4.1. BRAZIL
10.1.4.2. ARGENTINA
10.1.4.3. REST OF SOUTH AMERICA
10.1.5 MIDDLE EAST AND AFRICA
10.1.5.1. SOUTH AFRICA
10.1.5.2. SAUDI ARABIA
10.1.5.3. EGYPT
10.1.5.4. ISRAEL
10.1.5.5. KUWAIT
10.1.5.6. QATAR
10.1.5.7. REST OF MIDDLE EAST AND AFRICA
10.2 KEY PRIMARY INSIGHTS: BY MAJOR COUNTRIES
11. GLOBAL PROACTIVE SECURITY MARKET, COMPANY LANDSCAPE
11.1 COMPANY SHARE ANALYSIS: GLOBAL
11.2 COMPANY SHARE ANALYSIS: NORTH AMERICA
11.3 COMPANY SHARE ANALYSIS: EUROPE
11.4 COMPANY SHARE ANALYSIS: ASIA PACIFIC
11.5 MERGERS & ACQUISITIONS
11.6 NEW PRODUCT DEVELOPMENT & APPROVALS
11.7 EXPANSIONS
11.8 REGULATORY CHANGES
11.9 PARTNERSHIP AND OTHER STRATEGIC DEVELOPMENTS
12. GLOBAL PROACTIVE SECURITY MARKET, SWOT ANALYSIS
13. GLOBAL PROACTIVE SECURITY MARKET, COMPANY PROFILE
13.1 IBM
13.1.1 COMPANY SNAPSHOT
13.1.2 REVENUE ANALYSIS
13.1.3 PRODUCT PORTFOLIO
13.1.4 RECENT DEVELOPMENTS
13.2 CISCO
13.2.1 COMPANY SNAPSHOT
13.2.2 REVENUE ANALYSIS
13.2.3 PRODUCT PORTFOLIO
13.2.4 RECENT DEVELOPMENTS
13.3 MCAFEE, LLC
13.3.1 COMPANY SNAPSHOT;IA;
13.3.2 REVENUE ANALYSIS
13.3.3 PRODUCT PORTFOLIO
13.3.4 RECENT DEVELOPMENTS
13.4 PALO ALTO NETWORKS
13.4.1 COMPANY SNAPSHOT
13.4.2 REVENUE ANALYSIS
13.4.3 PRODUCT PORTFOLIO
13.4.4 RECENT DEVELOPMENTS
13.5 SECURONIX
13.5.1 COMPANY SNAPSHOT
13.5.2 REVENUE ANALYSIS
13.5.3 PRODUCT PORTFOLIO
13.5.4 RECENT DEVELOPMENTS
13.6 LOGRHYTHM, INC.
13.6.1 COMPANY SNAPSHOT
13.6.2 REVENUE ANALYSIS
13.6.3 PRODUCT PORTFOLIO
13.6.4 RECENT DEVELOPMENTS
13.7 RAPID7
13.7.1 COMPANY SNAPSHOT
13.7.2 REVENUE ANALYSIS
13.7.3 PRODUCT PORTFOLIO
13.7.4 RECENT DEVELOPMENTS
13.8 FIREEYE, INC
13.8.1 COMPANY SNAPSHOT
13.8.2 REVENUE ANALYSIS
13.8.3 PRODUCT PORTFOLIO
13.8.4 RECENT DEVELOPMENTS
13.9 ORACLE
13.9.1 COMPANY SNAPSHOT
13.9.2 REVENUE ANALYSIS
13.9.3 PRODUCT PORTFOLIO
13.9.4 RECENT DEVELOPMENTS
13.10 DELL, INC.
13.10.1 COMPANY SNAPSHOT
13.10.2 REVENUE ANALYSIS
13.10.3 PRODUCT PORTFOLIO
13.10.4 RECENT DEVELOPMENTS
13.11 QUALYS, INC.
13.11.1 COMPANY SNAPSHOT
13.11.2 REVENUE ANALYSIS
13.11.3 PRODUCT PORTFOLIO
13.11.4 RECENT DEVELOPMENTS
13.12 THREATCONNECT
13.12.1 COMPANY SNAPSHOT
13.12.2 REVENUE ANALYSIS
13.12.3 PRODUCT PORTFOLIO
13.12.4 RECENT DEVELOPMENTS
13.13 TRUSTWAVE HOLDINGS, INC.
13.13.1 COMPANY SNAPSHOT
13.13.2 REVENUE ANALYSIS
13.13.3 PRODUCT PORTFOLIO
13.13.4 RECENT DEVELOPMENTS
13.14 ALIENVAULT, INC. (AT&T CYBERSECURITY)
13.14.1 COMPANY SNAPSHOT
13.14.2 REVENUE ANALYSIS
13.14.3 PRODUCT PORTFOLIO
13.14.4 RECENT DEVELOPMENTS
13.15 FIREMON, LLC.
13.15.1 COMPANY SNAPSHOT
13.15.2 REVENUE ANALYSIS
13.15.3 PRODUCT PORTFOLIO
13.15.4 RECENT DEVELOPMENTS
13.16 FUJITSU
13.16.1 COMPANY SNAPSHOT
13.16.2 REVENUE ANALYSIS
13.16.3 PRODUCT PORTFOLIO
13.16.4 RECENT DEVELOPMENTS
13.17 DELINEA
13.17.1 COMPANY SNAPSHOT
13.17.2 REVENUE ANALYSIS
13.17.3 PRODUCT PORTFOLIO
13.17.4 RECENT DEVELOPMENTS
13.18 SWIMLANE INC.
13.18.1 COMPANY SNAPSHOT
13.18.2 REVENUE ANALYSIS
13.18.3 PRODUCT PORTFOLIO
13.18.4 RECENT DEVELOPMENTS
13.19 SKYBOX SECURITY, INC.
13.19.1 COMPANY SNAPSHOT
13.19.2 REVENUE ANALYSIS
13.19.3 PRODUCT PORTFOLIO
13.19.4 RECENT DEVELOPMENTS
13.20 SOFTSYS HOSTING
13.20.1 COMPANY SNAPSHOT
13.20.2 REVENUE ANALYSIS
13.20.3 PRODUCT PORTFOLIO
13.20.4 RECENT DEVELOPMENTS
NOTE: THE COMPANIES PROFILED IS NOT EXHAUSTIVE LIST AND IS AS PER OUR PREVIOUS CLIENT REQUIREMENT. WE PROFILE MORE THAN 100 COMPANIES IN OUR STUDY AND HENCE THE LIST OF COMPANIES CAN BE MODIFIED OR REPLACED ON REQUEST
14. RELATED REPORTS
15. QUESTIONNAIRE
16. ABOUT DATA BRIDGE MARKET RESEARCH

Research Methodology
Data collection and base year analysis are done using data collection modules with large sample sizes. The stage includes obtaining market information or related data through various sources and strategies. It includes examining and planning all the data acquired from the past in advance. It likewise envelops the examination of information inconsistencies seen across different information sources. The market data is analysed and estimated using market statistical and coherent models. Also, market share analysis and key trend analysis are the major success factors in the market report. To know more, please request an analyst call or drop down your inquiry.
The key research methodology used by DBMR research team is data triangulation which involves data mining, analysis of the impact of data variables on the market and primary (industry expert) validation. Data models include Vendor Positioning Grid, Market Time Line Analysis, Market Overview and Guide, Company Positioning Grid, Patent Analysis, Pricing Analysis, Company Market Share Analysis, Standards of Measurement, Global versus Regional and Vendor Share Analysis. To know more about the research methodology, drop in an inquiry to speak to our industry experts.
Customization Available
Data Bridge Market Research is a leader in advanced formative research. We take pride in servicing our existing and new customers with data and analysis that match and suits their goal. The report can be customized to include price trend analysis of target brands understanding the market for additional countries (ask for the list of countries), clinical trial results data, literature review, refurbished market and product base analysis. Market analysis of target competitors can be analyzed from technology-based analysis to market portfolio strategies. We can add as many competitors that you require data about in the format and data style you are looking for. Our team of analysts can also provide you data in crude raw excel files pivot tables (Fact book) or can assist you in creating presentations from the data sets available in the report.