Global Security Orchestration Market
Market Size in USD Billion
CAGR :
% 
 USD
3.60 Billion
USD
10.13 Billion
2024
2032
USD
3.60 Billion
USD
10.13 Billion
2024
2032
| 2025 –2032 | |
| USD 3.60 Billion | |
| USD 10.13 Billion | |
|
|
|
|
Security Orchestration Market Analysis
The security orchestration market is experiencing rapid growth, driven by increasing cyber threats, digital transformation, and the need for automated security solutions. Security orchestration integrates various security tools and processes, enhancing threat detection, response, and remediation capabilities. Organizations across industries such as BFSI, healthcare, IT and telecom, and government are adopting security orchestration, automation, and response (SOAR) solutions to streamline security operations and mitigate risks effectively. The rise in cloud adoption, IoT proliferation, and AI-driven threat intelligence has further accelerated market expansion. Advancements in AI, machine learning, and automation have strengthened security orchestration platforms, allowing faster and more accurate incident response. Companies are leveraging predictive analytics, behavioral analysis, and automated workflows to improve security posture and reduce manual intervention. North America dominates the market due to the presence of key industry players and advanced cybersecurity infrastructure, while the Asia-Pacific region is witnessing significant growth due to increasing cybersecurity awareness and digitalization initiatives. As cyber threats become more sophisticated, security orchestration solutions will continue evolving, ensuring seamless threat management and operational efficiency for enterprises worldwide.
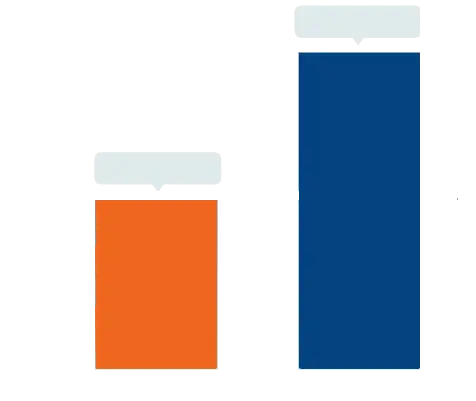
Security Orchestration Market Size
The global security orchestration market size was valued at USD 3.60 billion in 2024 and is projected to reach USD 10.13 billion by 2032, with a CAGR of 13.80% during the forecast period of 2025 to 2032. In addition to the market insights such as market value, growth rate, market segments, geographical coverage, market players, and market scenario, the market report curated by the Data Bridge Market Research team includes in-depth expert analysis, import/export analysis, pricing analysis, production consumption analysis, and pestle analysis.
Security Orchestration Market Trends
“Growing Adoption of AI-Driven Automation”
The security orchestration market is evolving rapidly, with AI-driven automation emerging as a key trend transforming threat response mechanisms. As cyber threats become more sophisticated, organizations are integrating artificial intelligence (AI) and machine learning (ML) into security orchestration, automation, and response (SOAR) platforms to enhance threat detection and remediation. AI-driven orchestration enables real-time threat intelligence, predictive analytics, and automated incident response, significantly reducing manual efforts and response time. For instance, IBM’s QRadar SOAR leverages AI to streamline security workflows, helping organizations detect and mitigate threats more efficiently. Similarly, Palo Alto Networks’ Cortex XSOAR integrates automation and AI-powered playbooks to improve threat response. The increasing adoption of cloud-based security solutions and IoT expansion further fuels the demand for AI-driven security orchestration. As cyberattacks grow in complexity, AI-powered security orchestration solutions will continue to drive market growth, ensuring proactive threat mitigation and operational resilience for enterprises worldwide.
Report Scope and Security Orchestration Market Segmentation
|
Attributes |
Security Orchestration Key Market Insights |
|
Segments Covered |
|
|
Countries Covered |
U.S., Canada and Mexico in North America, Germany, France, U.K., Netherlands, Switzerland, Belgium, Russia, Italy, Spain, Turkey, Rest of Europe in Europe, China, Japan, India, South Korea, Singapore, Malaysia, Australia, Thailand, Indonesia, Philippines, Rest of Asia-Pacific (APAC) in the Asia-Pacific (APAC), Saudi Arabia, U.A.E, South Africa, Egypt, Israel, Rest of Middle East and Africa (MEA) as a part of Middle East and Africa (MEA), Brazil, Argentina and Rest of South America as part of South America |
|
Key Market Players |
Musarubra US LLC (U.S.), Microsoft (U.S.), Intel Corporation (U.S.), Huawei Technologies Co., Ltd. (China), Splunk LLC (U.S.), Fortinet, Inc. (U.S.), Resolve Systems (U.S.), IBM (U.S.), Tufin (Israel), Swimlane Inc. (U.S.), Optiv Security Inc. (U.S.), Cyberbit (Israel), Palo Alto Networks (U.S.), Exabeam (U.S.), Acalvio Technologies Inc. (U.S.), Digital.AI (U.S.), Baffle (U.S.), and Comcast (U.S.) |
|
Market Opportunities |
|
|
Value Added Data Infosets |
In addition to the market insights such as market value, growth rate, market segments, geographical coverage, market players, and market scenario, the market report curated by the Data Bridge Market Research team includes in-depth expert analysis, import/export analysis, pricing analysis, production consumption analysis, and pestle analysis. |
Security Orchestration Market Definition
Security orchestration refers to the process of integrating and automating various security tools, systems, and processes to streamline threat detection, incident response, and remediation. It enables security teams to manage and coordinate workflows across multiple cybersecurity solutions, enhancing efficiency and reducing response time.
Security Orchestration Market Dynamics
Drivers
- Rising Cyber Threats and Sophisticated Attacks
The increasing frequency and complexity of cyber threats, such as ransomware, phishing, and advanced persistent threats (APTs), are major drivers of the security orchestration market. Cybercriminals are leveraging AI-driven malware, zero-day exploits, and social engineering tactics to bypass traditional security defenses, making automated threat detection and response crucial. For instance, in 2021, the Colonial Pipeline ransomware attack severely disrupted fuel supply chains in the U.S., highlighting the need for faster and more efficient security incident response. Security orchestration platforms help organizations respond to such incidents by integrating real-time threat intelligence, automated workflows, and incident correlation to mitigate risks proactively. As cyberattacks continue to evolve, businesses are increasingly adopting SOAR solutions to automate security operations, minimize downtime, and enhance cybersecurity resilience, fueling market growth.
- Growing Adoption of SOAR Solutions
Organizations are increasingly implementing Security Orchestration, Automation, and Response (SOAR) solutions to streamline security operations and improve incident response efficiency. SOAR platforms enable security teams to centralize security tools, automate repetitive tasks, and prioritize threat responses based on severity. For instance, IBM QRadar SOAR automates threat intelligence sharing and speeds up incident triage, reducing response time significantly. In addition, Palo Alto Networks’ Cortex XSOAR integrates with multiple security systems, allowing teams to orchestrate workflows and improve collaboration. With the growing attack surface due to cloud adoption, IoT proliferation, and hybrid work models, enterprises need scalable and intelligent security solutions. The ability of SOAR to reduce human intervention, improve threat visibility, and enhance compliance is driving its adoption across industries such as BFSI, healthcare, and government, further propelling the security orchestration market forward.
Opportunities
- Increasing Advancements in AI, Machine Learning and Automation
The integration of artificial intelligence (AI), machine learning (ML), and automation in security orchestration presents a significant market opportunity by enhancing threat detection, incident response, and decision-making processes. AI-driven security orchestration enables real-time threat intelligence, predictive analytics, and automated incident response, reducing manual intervention and improving efficiency. For instance, Exabeam’s AI-powered SIEM and security analytics platform leverages behavioral analytics to detect anomalies and automate response actions, preventing data breaches before they escalate. Similarly, Microsoft Sentinel, a cloud-native SIEM and SOAR platform, applies ML algorithms to identify and prioritize threats dynamically. As cyber threats become more sophisticated, businesses are increasingly adopting AI-powered security orchestration, automation, and response (SOAR) solutions to streamline security workflows, enhance operational efficiency, and reduce response time. The growing reliance on AI and ML in cybersecurity solutions presents a lucrative opportunity for security orchestration vendors to innovate and expand their offerings, driving market growth.
- Expansion of Cloud Computing and IoT Devices
The rapid adoption of cloud computing and the proliferation of IoT devices have significantly expanded the attack surface, creating a strong demand for automated security orchestration solutions. As businesses migrate to cloud environments and deploy IoT-connected devices, they face increased risks such as misconfigurations, unauthorized access, and data breaches. Security orchestration solutions help mitigate these risks by integrating cloud security tools, automating policy enforcement, and enabling real-time threat detection. For instance, Palo Alto Networks' Prisma Cloud provides automated security for multi-cloud environments, ensuring compliance and reducing vulnerabilities. Similarly, Cisco’s SecureX integrates security orchestration with cloud-native security tools to enhance visibility across distributed environments. With the continued expansion of remote work, edge computing, and IoT ecosystems, organizations are actively seeking scalable and automated security solutions. This trend presents a significant growth opportunity for security orchestration providers to develop cloud-native and IoT-compatible security solutions, catering to evolving enterprise needs.
Restraints/Challenges
- High Implementation Costs
The adoption of Security Orchestration, Automation, and Response (SOAR) platforms often requires significant upfront investment, making it a barrier for many organizations, especially small and mid-sized enterprises (SMEs). Costs include software licensing, infrastructure upgrades, and customization to align with existing security workflows. In addition, ongoing maintenance and updates demand further financial commitments. For instance, a large financial institution implementing a SOAR platform may need to integrate it with SIEM (Security Information and Event Management) systems, threat intelligence feeds, endpoint detection, and cloud security solutions, leading to additional expenses for APIs, connectors, and third-party service fees. The high cost of ownership discourages many companies from adopting these solutions, slowing market expansion and leading to hesitancy in security automation adoption.
- Shortage of Skilled Cybersecurity Professionals
The shortage of skilled cybersecurity professionals proficient in SOAR solutions is a major obstacle for the Security Orchestration Market. SOAR platforms require expertise in security automation, incident response, threat intelligence, and scripting languages (Python for playbook development). However, the demand for SOAR-skilled professionals far exceeds the supply, creating a talent gap that limits adoption. For instance, a healthcare organization implementing security orchestration may struggle to find in-house experts to configure automation rules and manage security incidents efficiently. As a result, companies often rely on external consultants or managed security service providers (MSSPs), further increasing costs and delaying the full realization of orchestration benefits. The lack of skilled personnel hinders market growth, as organizations either delay adoption or fail to maximize the platform’s potential.
This market report provides details of new recent developments, trade regulations, import-export analysis, production analysis, value chain optimization, market share, impact of domestic and localized market players, analyses opportunities in terms of emerging revenue pockets, changes in market regulations, strategic market growth analysis, market size, category market growths, application niches and dominance, product approvals, product launches, geographic expansions, technological innovations in the market. To gain more info on the market contact Data Bridge Market Research for an Analyst Brief, our team will help you take an informed market decision to achieve market growth.
Security Orchestration Market Scope
The market is segmented on the basis of components, application, deployment model, organization size, and industry vertical. The growth amongst these segments will help you analyse meagre growth segments in the industries, and provide the users. The growth amongst these segments will help you analyze meagre growth segments in the industries and provide the users with a valuable market overview and market insights to help them make strategic decisions for identifying core market applications.
Component
- Solution
- Services
- Others
Application
- Threat Intelligence
- Network Forensics
- Others
Deployment Mode
- Cloud
- On-Premises
Organization Size
- Small and Medium Enterprises (SMEs)
- Large Enterprises
Industry Vertical
- BFSI
- Energy and Utilities
- Government
- Healthcare
- Retail
- IT and Telecom
- Others
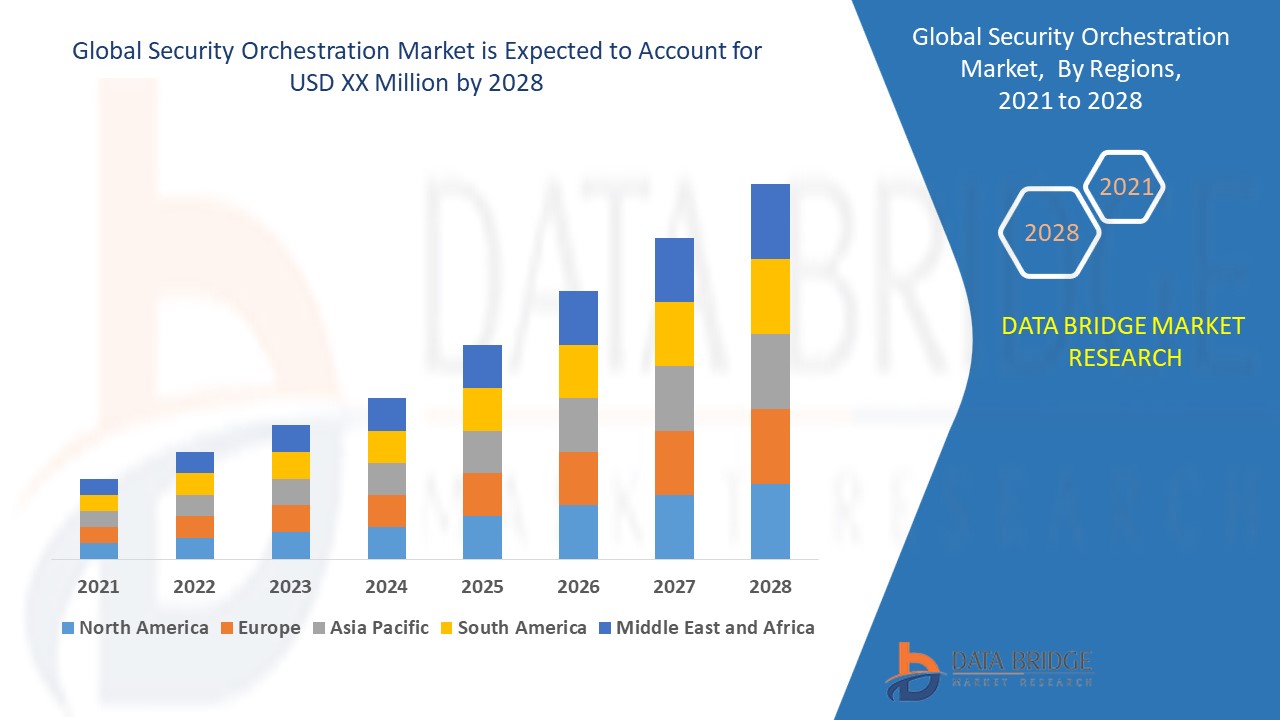
Security Orchestration Market Regional Analysis
The market is analyzed and market size insights and trends are provided by country, components, application, deployment model, organization size, and industry vertical. The growth amongst these segments will help you analyse meagre growth segments in the industries, and provide the users as referenced above.
The countries covered in the market report are U.S., Canada, Mexico in North America, Germany, Sweden, Poland, Denmark, Italy, U.K., France, Spain, Netherland, Belgium, Switzerland, Turkey, Russia, Rest of Europe in Europe, Japan, China, India, South Korea, New Zealand, Vietnam, Australia, Singapore, Malaysia, Thailand, Indonesia, Philippines, Rest of Asia-Pacific (APAC) in Asia-Pacific (APAC), Brazil, Argentina, Rest of South America as a part of South America, U.A.E, Saudi Arabia, Oman, Qatar, Kuwait, South Africa, Rest of Middle East and Africa (MEA) as a part of Middle East and Africa (MEA).
North America dominates the security orchestration market primarily due to the widespread availability of cost-effective cloud-based security solutions. The region benefits from advanced cybersecurity infrastructure and a strong presence of key market players. In addition, increasing incidents of sophisticated cyber-attacks are driving the demand for enhanced security automation. This growing need for robust security measures is expected to fuel market expansion in North America during the forecast period.
Asia-Pacific is expected to witness fastest growth in the security orchestration market, driven by increasing digital transformation initiatives. A large number of SMEs in the region are actively adopting security orchestration strategies to safeguard their operations from evolving cyber threats. In addition, government support for cybersecurity advancements and rising investments in cloud-based security solutions are contributing to market expansion. As cyber threats become more sophisticated, the demand for automated security solutions in Asia-Pacific is set to grow significantly.
The country section of the report also provides individual market impacting factors and changes in market regulation that impact the current and future trends of the market. Data points such as down-stream and upstream value chain analysis, technical trends and porter's five forces analysis, case studies are some of the pointers used to forecast the market scenario for individual countries. Also, the presence and availability of global brands and their challenges faced due to large or scarce competition from local and domestic brands, impact of domestic tariffs and trade routes are considered while providing forecast analysis of the country data.
Security Orchestration Market Share
The market competitive landscape provides details by competitor. Details included are company overview, company financials, revenue generated, market potential, investment in research and development, new market initiatives, global presence, production sites and facilities, production capacities, company strengths and weaknesses, product launch, product width and breadth, application dominance. The above data points provided are only related to the companies' focus related to market.
Security Orchestration Market Leaders Operating in the Market Are:
- Musarubra US LLC (U.S.)
- Microsoft (U.S.)
- Intel Corporation (U.S.)
- Huawei Technologies Co., Ltd. (China)
- Splunk LLC (U.S.)
- Fortinet, Inc. (U.S.)
- Resolve Systems (U.S.)
- IBM (U.S.)
- Tufin (Israel)
- Swimlane Inc. (U.S.)
- Optiv Security Inc. (U.S.)
- Cyberbit (Israel)
- Palo Alto Networks (U.S.)
- Exabeam (U.S.)
- Acalvio Technologies Inc. (U.S.)
- Digital.AI (U.S.)
- Baffle (U.S.)
- Comcast (U.S.)
Latest Developments in Security Orchestration Market
- In May 2022, Bugcrowd collaborated with IBM to connect to the security orchestration, automation, and response space with IBM Resilient integration. IBM Resilient is a system used by security teams for automating and managing security responses
- In May 2022, Palo Alto Networks announced a collaboration with Cohesity, integrating its SOAR platform with Cohesity’s AI-driven data management platform to significantly reduce customers' ransomware risks
- In March 2022, Ridge Security partnered with Splunk to enhance response speed and improve the effectiveness of security teams. The integration of RidgeBot’s API into Splunk SOAR strengthens cybersecurity defenses
- In July 2021, Rapid7 acquired threat intelligence leader IntSights, enabling integrations between the IntSights External Threat Protection Suite and Rapid7’s Insight portfolio for enhanced security capabilities
- In September 2020, ThreatConnect acquired Nehemiah Security, adding Cyber Risk Quantification capabilities to its existing SOAR platform to improve risk assessment and threat response
SKU-
Get online access to the report on the World's First Market Intelligence Cloud
- Interactive Data Analysis Dashboard
- Company Analysis Dashboard for high growth potential opportunities
- Research Analyst Access for customization & queries
- Competitor Analysis with Interactive dashboard
- Latest News, Updates & Trend analysis
- Harness the Power of Benchmark Analysis for Comprehensive Competitor Tracking
Research Methodology
Data collection and base year analysis are done using data collection modules with large sample sizes. The stage includes obtaining market information or related data through various sources and strategies. It includes examining and planning all the data acquired from the past in advance. It likewise envelops the examination of information inconsistencies seen across different information sources. The market data is analysed and estimated using market statistical and coherent models. Also, market share analysis and key trend analysis are the major success factors in the market report. To know more, please request an analyst call or drop down your inquiry.
The key research methodology used by DBMR research team is data triangulation which involves data mining, analysis of the impact of data variables on the market and primary (industry expert) validation. Data models include Vendor Positioning Grid, Market Time Line Analysis, Market Overview and Guide, Company Positioning Grid, Patent Analysis, Pricing Analysis, Company Market Share Analysis, Standards of Measurement, Global versus Regional and Vendor Share Analysis. To know more about the research methodology, drop in an inquiry to speak to our industry experts.
Customization Available
Data Bridge Market Research is a leader in advanced formative research. We take pride in servicing our existing and new customers with data and analysis that match and suits their goal. The report can be customized to include price trend analysis of target brands understanding the market for additional countries (ask for the list of countries), clinical trial results data, literature review, refurbished market and product base analysis. Market analysis of target competitors can be analyzed from technology-based analysis to market portfolio strategies. We can add as many competitors that you require data about in the format and data style you are looking for. Our team of analysts can also provide you data in crude raw excel files pivot tables (Fact book) or can assist you in creating presentations from the data sets available in the report.